Luggage Scanning x-ray machine Xray security equipment (SECUPLUS SPX-5030B)/X-ray Baggage Inspection Scanner and Xray security equipment
SPX-6040 X-ray Security Inspection Equipment for mail, parcels, handbags, briefcases, baggage etc. It can detect contraband, weapons, dangerous and illegal items.
SPX-6040 is based on user-friendly design with ergonomic operator control panel and adjustable control panel stand. It is widely used in the areas of critical infrastructure, government buildings, public transportation, international events, aviation, venues or hotels.
| Tunnel Size | 500(W)*300(H)mm |
| Conveyor Speed | 0.2m/s |
| Conveyor Max Load | 170kg |
| Dose per Inspection | <2.9μ Gy/h |
| Resolution | <0.101mm Metal Wire |
| Spatial resolution | Level: Dia1.0mm, Vertical: Dia1.3mm |
| Penetrate resolution | Dia 0.511mm |
| Penetration | 38-40mm steel |
| Film Safety | Guarantee ISO1600 Film |
| X-ray Leakage | <0.5 μ Gy/h (at a distance of 5cm From external housing) |
| Image System : | |
| Technical Principle | Dual-energy X-ray Imaging; L Shaped Array |
| X-ray Sensor | L-Shaped Photodiode Array (multi-energetic) |
| Monitor | High Resolution Color, LCD Accord, 17inch |
| Image Display | High resolution of 1024 * 1280 pixel; Image Grey Level: 65536 |
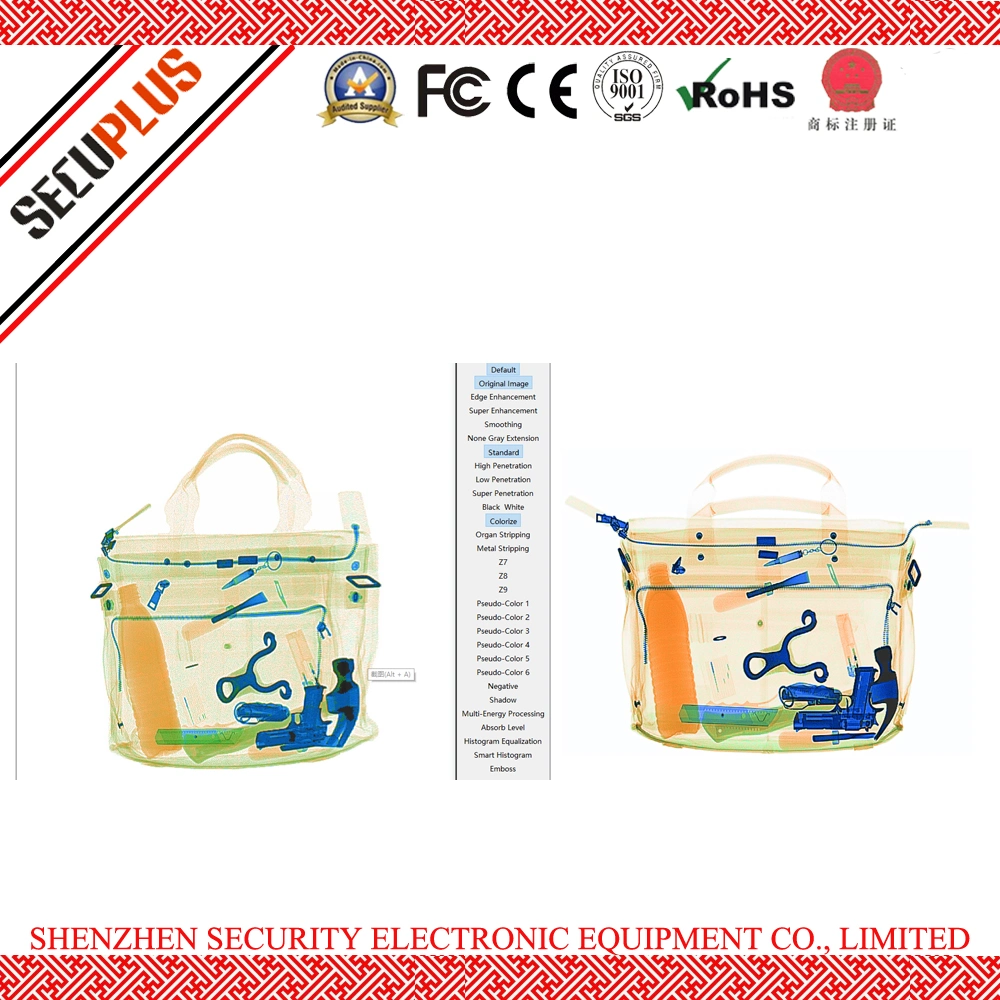
| Image Enhancement | 1-64times enlargement continuity, Color/BW, negative, high/low penetration, organic /inorganic Stripping, general enhancement, and pseudo color, etc. |
| Image Recall: | All preceding images recallable, retrieval. |
| Explosives & Narcotics Detection | Explosives & narcotics alarm and highlight according to atomic number signature |
| High Density Region Alarm | Impenetrable region alarm and highlight, for possible concealing of threats and contrabands |
| Image Archive | Up to 100,000 images stored automatically, enable transferring to USB disk, and converting to JPG, BMP and other general formats |
| Miscellaneous Functions | Time/date display, counters, user management, system-on/X-ray-on timers, power on self test, built-in diagnostic facilities, dual-direction scanning, system log, system standby and stimulant training,etc |
| Network Applications | Multiple remote applications available based on Ethernet LAN and windows platform, such as image centralized storage and identify, recheck workstation, and network TIP, etc ( Optional) . |
| Images process | 24bit real time processing ,4colors analysis, Images displayed marked date and ID NO ,Count the number of bags ,Memory gray level:65536 |
| Operating Environment: | |
| Operation temperature/Humidity | 0ºC-40ºC/10%-95%(non-condensing) |
| Storage Temperature/Humidity | -20ºCto 60ºC/ 5%-95%(non-condensing) |
| Operation Power | 220VAC(±10%)50±3Hz (Optional: 100VAC,110VAC,120VAC,200VAC) |
| Power Consumption | 1.0KW (max), 0.7KW(working) |
| Noise | <58db |
| Scanner Dimensions (L×W×H) | 2007.5mm x868mm x1314 mm |
| Gross Weight | 600kgs |
| Packing Volume | 3.5 CBM |
| X-ray Generator: | |
| Anode Voltage | 160kv |
| Anode Power | 0.35 MA |
| Generate angle | 80 degree upward |
| Brand | Chinese Brand |
| Generate direct | from bottom to top |
| Cooling / Duty Cycle | Oil Cooling /100 |
Product highlights:
* Multilingual operation
* Automatic built in test and self diagnosis
* Secure access Key
* Continuous working 10000 hours above
* Threat alert and material classification
* International standard configuration:
Japan Hammatsu detection and UK Sens-tech board
* Network‐Ready
* Energy saving design
* One key turn off
* Drugs and explosives inspection
* Indication of the date and time
RFQ:
Are you manufacturer?
Yes, we are professsional manufacturer of security threats detection system in south of China.
Stable quality and foremost service always be the key that we focus on.
How many days we can get the machine after payment?
Normally, with stock only need 3-5 days for leading time.
Without stock, need 10-15 days to manage the production.
Delivery by sea, air for your choices.
How about the warranty and services?
Provide one year warranty and lifetime technic support.
Accept to send our engineer to your country for training in additional cost.
Free training one-on-one in our factory for free.
We strive to bridge the gap between requirements and technology worldwide with practical, innovative and high technology readiness solutions. The future, we want to become the leading supplier of large-scale security equipment industry, with our products help to achieve the 'Safer country, Safer world. "
SECUPLUS Commitment:
We are committed and driven to provide both public and private sectors with:
- In-depth understanding of end-user demands, market trends and future challenges.
- Intimate relationships with leaders in the security industry and technology providers
- Creation of the optimal end-to-end bridging solution that meets each operational challenge